Cyber Compliance Chutes & Ladders
This article first appeared on The Risk Realist Newsletter.
TL;DR: The Delve incident is a symptom of a broken system, and the real fix is to treat compliance reports as truthful representations of a well-run program—not as badges bought through automation and bargain audits.
Not Surprised, Just Disappointed
The Delve situation didn’t surprise anyone who’s been close to how program and process development, compliance, and automation actually work. It surprised people who believed the marketing.
There’s a meaningful difference. I’m unpacking it this week—not to pile on a company that’s already down, but because the compliance business model that enabled it is alive and well across the industry. If you look at the competing firms, you’ll find very similar (if not identical) marketing claims, promises, and incentive structures that reward speed and volume over quality.
This isn’t a coincidence. It’s a market dynamic and a set of skewed incentives and pressures for SaaS startups. And it deserves an honest conversation. Most importantly, we need to equip SaaS leaders and the enterprise customers that manage third party risk with knowledge to navigate the challenges.
I have worked on multiple sides of the table, managing vendor risk inside a large enterprise, consulting for organizations and helping them build cyber programs to get audit-ready, and independently advising security leaders on how to evaluate the reports they receive. Here’s the view from each seat so we can understand each other better, and grow as an industry:
- From the enterprise risk management seat: You’re managing hundreds, sometimes thousands of third-party relationships. You send questionnaires, but you get back thin answers, binary responses, and documents clearly produced with haste. You know the report you’re holding may not reflect the actual state of controls, especially not specific to your organization’s data and how the vendor is supporting you. But you don’t have the bandwidth to verify or audit it, so you accept it and move on. The checkbox gets checked, and we all grumble about the limited value of third-party risk program management.
- From the startup or mid-market seat: You’re not trying to build a fake security program. You’re trying to build a product, acquire customers, and survive... with limited funding! Security feels like a tax or something you hope to defer until the next seed round... and compliance feels like an even higher tax. You hire whoever is cheapest, fastest, and maybe willing to not go “too deep,” because you need the badge more than you need the understanding.
- From the compliance automation and audit firm seat: You’re competing on price in a market that has commoditization attestation. You have to win on cost. The business math simply doesn’t support deep, hands-on program development work at the rates the market demands.
Once we recognize the priorities each seat deals with—lack of bandwidth, lack of funding, the need to drive revenue—we can zoom back out. It makes sense now; the system is set up to produce exactly the outcomes we’re all seeing and complaining about.
The Year One Trap (or, SOC it to Me?)
Here’s the specific failure pattern I see most often.
A startup leadership team authorizes a “Hail Mary” preparatory effort three to four months before they need a SOC 2 report. They bring in a firm (often whoever is cheapest), run heroic discovery sessions, document everything in a sprint, build policies from templates, and implement controls just long enough to pass the audit window.
They pass.
Everyone celebrates.
Then the exhaustion hits. The policies written as compliance artifacts quietly stop being followed, if they were even communicated and followed to begin with. The vendor review process that was manually executed during audit prep reverts to an unmanaged backlog of box checking. The monthly access reviews? Nobody remembers to schedule them. The audit firm moves on to their next client.
Year Two starts with an audit gap letter. The performance period needed to be delayed because the people and processes stopped working on the in-scope controls. Now the organization is paying again in the currencies of time, money, and team capacity to rebuild what they already built.
The math is brutal. What organizations spend on the Year One sprint plus the Year Two remediation often dramatically exceeds what a properly scoped foundational program engagement would have cost.
It’s like taking a shortcut... and adding ten miles to your original five-mile trip. Then the attestation sandwich is served.
Now let’s talk about what happens to the organization three years into this cycle of compliance re-work, wondering why it keeps getting more expensive.
Their initial SOC 2 scope was a reasonable General Controls review. SOC 2 Type I, then Type II. Done. Badge earned.
Then the first healthcare customer arrives. They want HIPAA controls coverage. “No problem,” you say. Except HIPAA certification doesn’t exist, so now you’re building out Privacy and Security Rule controls and figuring out how to include coverage in your SOC 2 scope.
A HITRUST acolyte customer shows up next. HITRUST is a significant investment. The framework is comprehensive, the assessment process is rigorous, and the pay-to-play licensing structure means you’re spending money before you’ve aligned a single policy to the HITRUST standards.
Next, European customers want ISO 27001. Your Japan-based customers may have a similar ask. ISO 27001 is genuinely excellent, but implementing and maintaining it is real work, and now you’re building again.
You’re growing. You win some state government contract. Now TX-RAMP or StateRAMP (now GOVRAMP) is on the table. More pay-to-play. More documentation. More assessment cycles.
And then one of your business lines touches a DoD contract. CMMC requirements were finalized into law in late 2024, and this is not a questionnaire you can answer on a weekend. Level 2 certification requires a third-party assessment organization (C3PAO) to come in and verify.
Add it up: SOC 2, HIPAA/SOC 2 Privacy, HITRUST, ISO 27001, TX-RAMP/GOVRAMP, CMMC. Six or seven frameworks. Each with its own assessment cycle, its own documentation requirements, and its own third-party assessment cost. The business case of taking a one-by-one serial approach to compliance as your attestation sandwich is served will likely be a 10x multiple on your investment as you’re trying to grow your company in comparison to building a risk-based cyber program from the ground up before running the compliance gauntlet. And the cost of staff churn, burnout, and compliance fatigue is the bigger cost.
How to Actually Win This Game
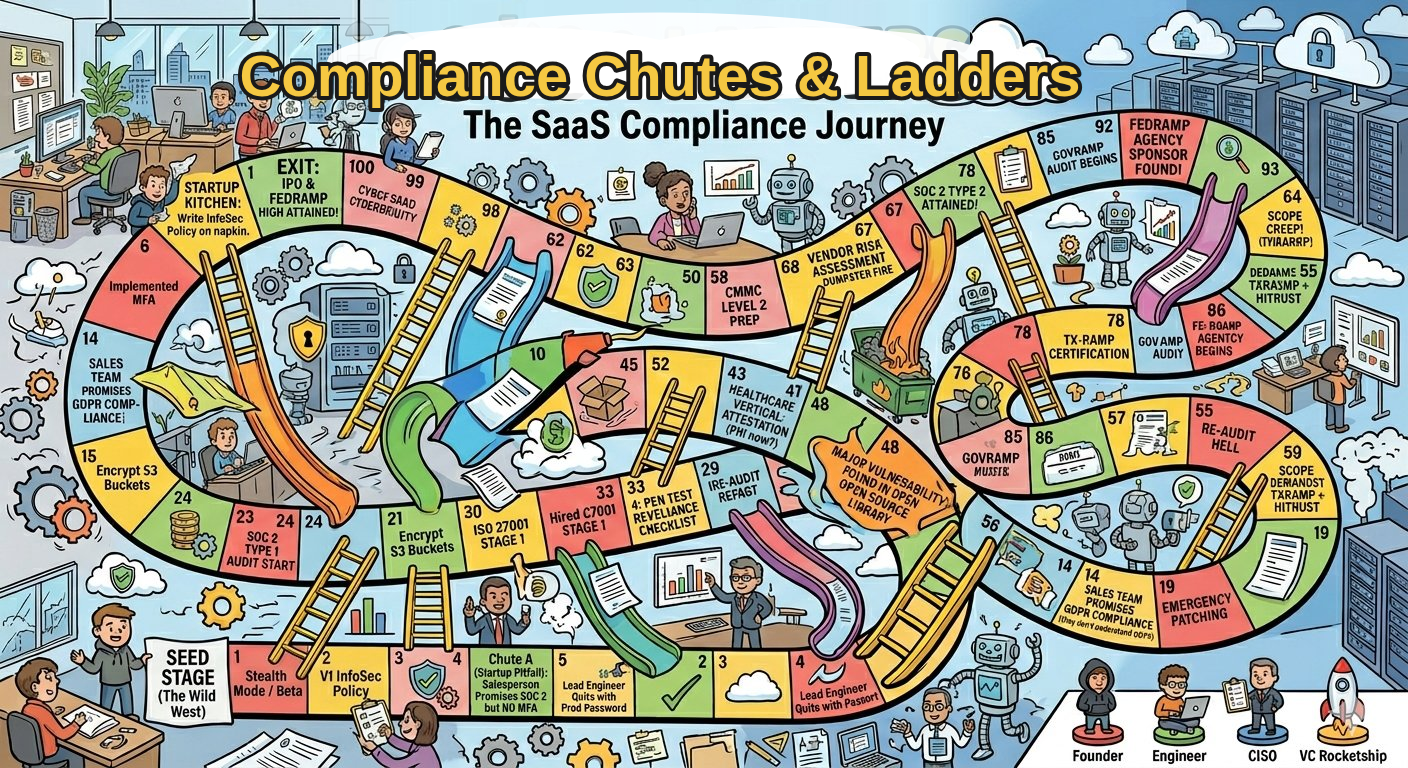
The title of this edition wasn’t chosen for fun. Compliance Chutes & Ladders is an accurate metaphor for how most SaaS companies and startups experience compliance, and most are playing it ad-hoc and sliding down every costly chute.

Here’s the shift in thinking I’d recommend:
1. Stop treating each framework as a separate project or ad-hoc customer requirement.
The organizations managing a multi-framework compliance stack effectively are the ones that built a control architecture first. When your foundational controls are designed around NIST CSF or a similar common framework, and you think about effective operational processes vs audit evidence, you’re mapping controls to certifications rather than building separate programs for each one. This makes an enormous difference in long-term cost and sustainability.
2. Build the program, not the report.
The compliance report is evidence the controls exist. Organizations trying to produce the evidence without the program spend more in every audit cycle, indefinitely, than organizations that built the program once and let the evidence flow from it.
3. Sequence your frameworks deliberately.
If you know HITRUST is in your future because you’re going after health system customers who subscribe to it, work backward from there. NIST or a common controls framework can serve as a foundation. The control overlap between SOC 2, HIPAA, and HITRUST is significant when you have built them to align. Do it in the wrong order, or in isolation, and you rebuild rather than extend.
4. Pick your audit partners for longevity, not price.
The cheapest SOC 2 audit today may produce a report your next auditor has to disclaim. Auditor quality variance is real, and when a sophisticated enterprise customer sends their own security team to review your report, they’ll notice it. Invest in relationships with firms that will still be credible three years from now. And more importantly, pick a firm that will be credible to your customers. Remember, anyone can Google around and find the same information; and an $8k SOC 2 audit guaranteed in three days doesn’t impress anyone who knows what a cyber program needs to entail or is responsible for managing 3rd party risk.
5. Know what “pay to play” is costing you before you commit.
HITRUST, StateRAMP/GOVRAMP, and FedRAMP are not free frameworks. They are operated by commercial, for-profit businesses, and they have licensing costs, authorized assessor requirements, and annual maintenance fees that compound. Before a sales team commits a customer to one of these paths, finance and security leadership need to be in the room doing the math.

What This Has to Do with Delve
The Delve situation is a symptom of a system that optimized for the wrong things: speed and low cost over quality and sustainability.
The organizations that ended up with a compromised audit artifact were not uniquely reckless. They were doing what the market told them was acceptable. The market was wrong.
You’re not buying a badge. You’re representing the state of your security controls to every customer who evaluates you. Building a program scalable to your immediate and future needs is a “slow down to go fast” play. In the long run, your overall investment and organizational burn will be better in growing a foundation placed on level ground.
That’s worth taking seriously.
Questions about building a multi-framework program/compliance approach without breaking your team or your budget? Reach out at info@revealrisk.com.
Aaron Pritz, CEO — Reveal Risk
The Risk Realist publishes weekly on LinkedIn. Subscribe to get each edition delivered to your feed.
 Aaron Pritz
Aaron Pritz




