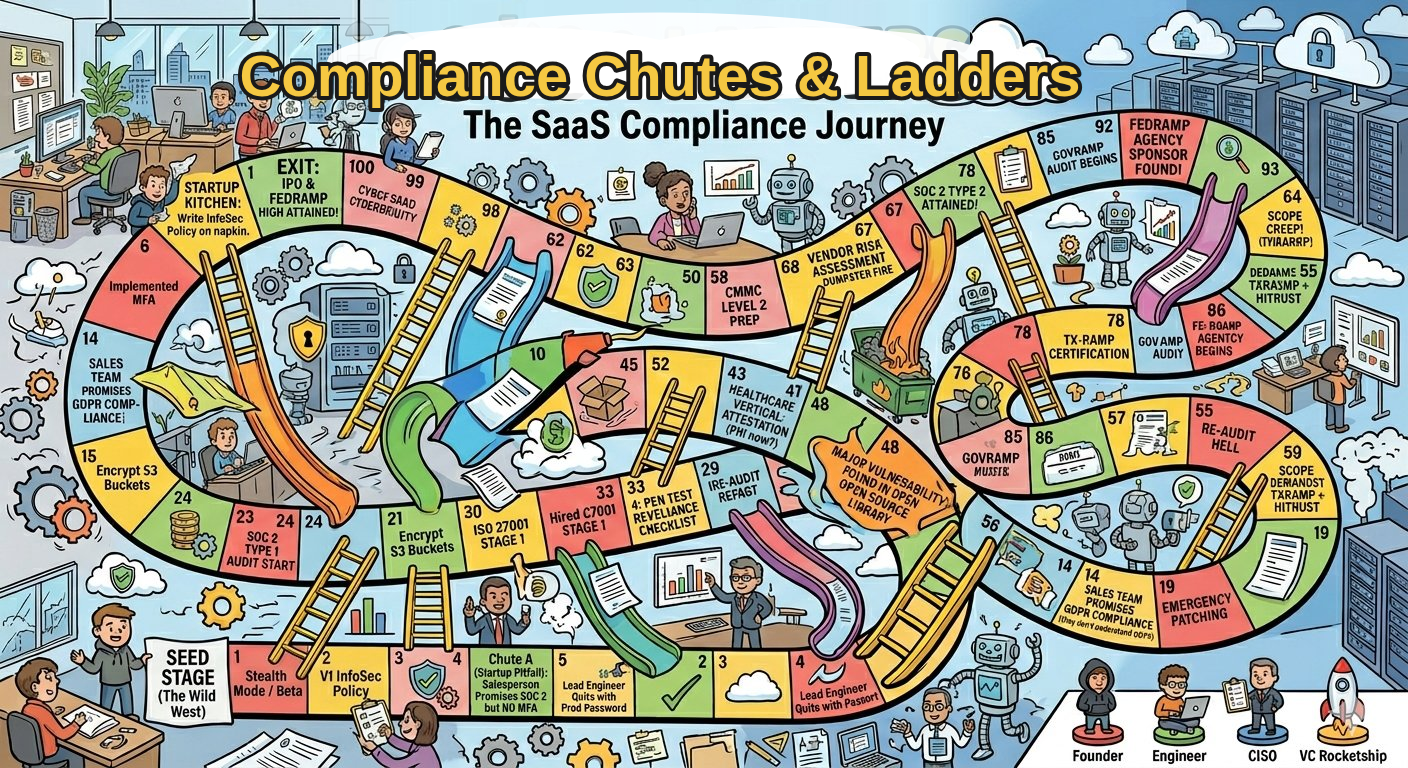
Security failures are rarely caused by a lack of awareness. They happen because insecure workflows are often the fastest path to getting work done.
What Security Teams Expect vs. What Actually Happens
What security teams expect:
- Employees follow secure processes
- Policies guide behavior
- Training changes behavior
- Employees find faster workarounds
- Policies don’t match real workflows
- Behavior follows incentives and friction
When the path of least resistance is insecure, training alone will never fix the problem.