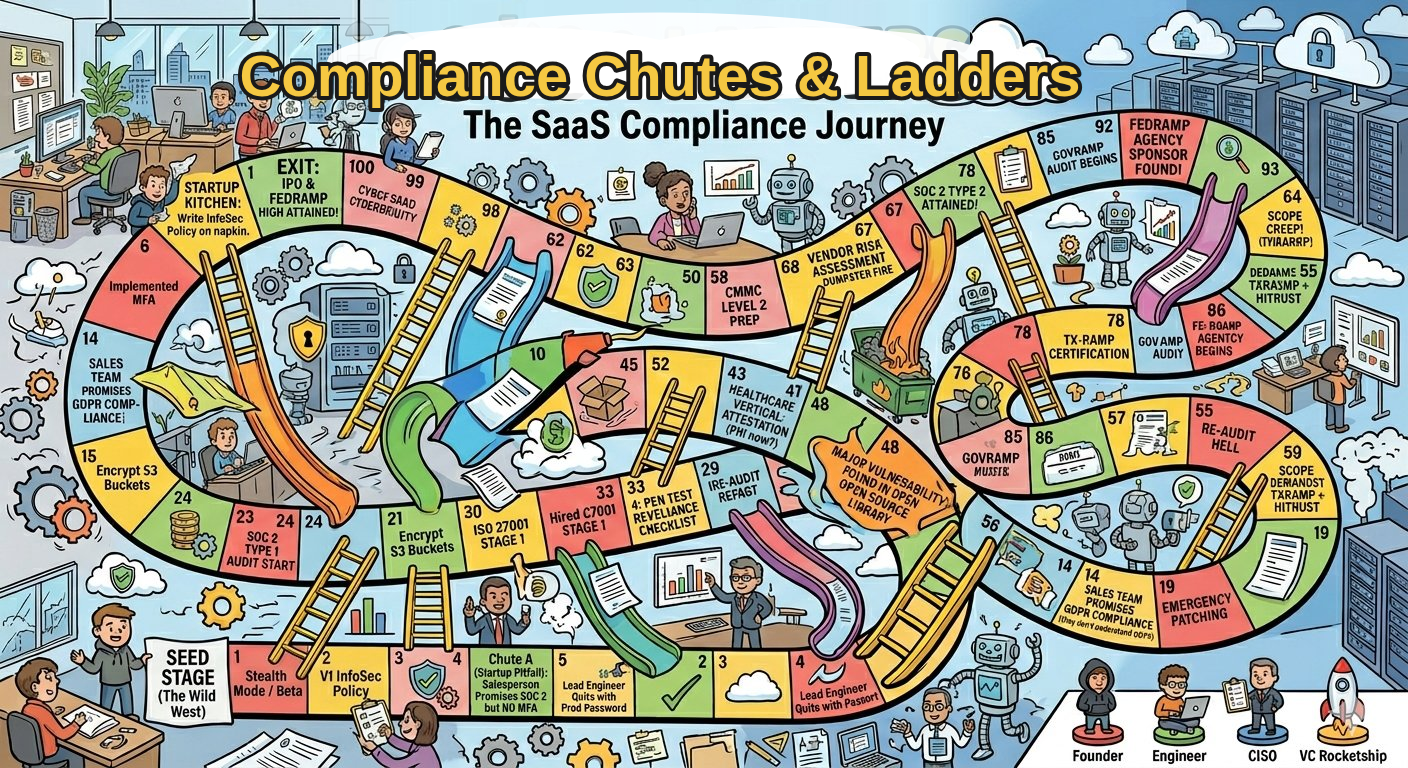
Common realities inside organizations:
- employees must open emails from unknown senders to do their job
- insecure workflows are faster than secure ones
- security teams operate separately from business operations
- awareness programs prioritize compliance instead of risk reduction
When the fastest way to get work done is insecure, training alone will never fix the problem.
Human Risk Management focuses on redesigning systems so secure behavior becomes the default.

.webp?width=2000&name=Rectangle%2063%20(8).webp)